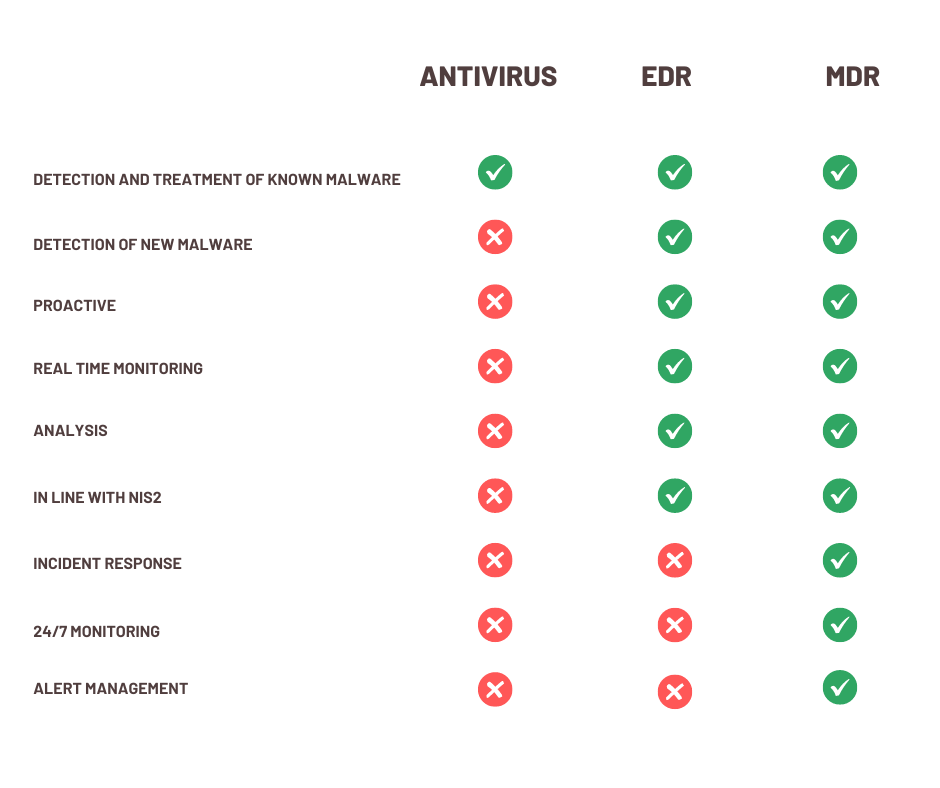
Traditional antivirus software is no longer sufficient to protect organizations against modern cyber threats. Endpoint Detection & Response (EDR) and Managed Detection & Response (MDR) are used to continuously monitor, detect, and respond to suspicious activity on endpoint devices, in line with zero-trust security principles and regulatory requirements such as NIS2.
The European NIS2 (Network and Information Systems Directive) regulations support this zero-trust concept. That’s why these guidelines aim at improving cybersecurity in various sectors in European member states. NIS2 wants to increase resilience and encourages broader implementation of security measures in different sectors.
What Is Endpoint Detection & Response (EDR)?
Endpoint Detection & Response (EDR) is an advanced tool designed to monitor endpoint devices such as desktops, laptops and servers. It will detect and respond to cyber threats. This technology replaces traditional antivirus software such as Trend Micro or Bitdefender and provides better protection.
Endpoint Detection & Response (EDR) and Managed Detection & Response (MDR) play a crucial role in meeting the heightened security standards.
How Is EDR Different from Traditional Antivirus Software?
What Does Antivirus Software Do?
Antivirus software is designed to detect, prevent, and remove malware by comparing files against a database of known threat signatures.
A good homeowner does not rely solely on a locked door to protect his home from a burglar. Similarly, organizations should not rely solely on traditional antivirus software to protect their endpoints from cyber threats. While antivirus can act as a basic lock, it only keeps out known intruders.
Key characteristics of antivirus software:
- Designed to detect, prevent, and remove malware by scanning files against a database of known malware signatures.
- Reactive in nature, relying on signature-based detection methods.
- Provides basic remediation options like quarantine or deletion.
- Effective against common threats but can struggle with new or sophisticated attacks.
What Does EDR Do Instead?
Endpoint Detection & Response (EDR) functions as an advanced security system with motion sensors, cameras and alarms. It not only keeps known risks at bay, but actively monitors for suspicious behavior and responds in real time to potential threats, giving your organization extra protection.
Key characteristics of EDR solutions:
- Real-time monitoring: continuous monitoring of endpoints to detect potential threats.
- Advanced threat detection: EDR uses behavioral analysis, anomaly detection and machine learning to identify a wide range of known and unknown threats such as zero-day exploits and advanced threat protection (ATPs).
- In-depth analysis: EDR continuously collects and analyzes data from endpoints which provides deep insight into endpoint activity and can be supportive in forensic investigations.
- Incident and response possibilities: detailed investigation, threat detection and automated responses are possible to mitigate threats in real time.
- Proactive defense: EDR systems proactively search for potential threats
- Regulatory compliance: essential for meeting security standards imposed by guidelines such as NIS2.
Why Is EDR Relevant in a Zero-Trust Security Model?
Zero trust is a security approach that assumes no device or user is trusted by default.
EDR supports zero-trust principles by continuously validating endpoint activity rather than assuming endpoints are safe once connected. This aligns with the goals of the NIS2 directive, which aims to improve cybersecurity resilience across European member states and sectors.
What Is Managed Detection & Response (MDR)?
Managed Detection & Response (MDR) is a security service that combines EDR technology with continuous monitoring and analysis by security experts.
This managed layer provides additional assurance because it helps differentiate between identified risks. MDR ensures that the real threats are addressed immediately.
How Does MDR Build on EDR?
EDR provides the technology to detect threats. MDR adds human expertise to interpret and act on those detections.
Key aspects of MDR include:
- 24/7 monitoring: Around-the-clock surveillance by security experts.
- Alert management: Efficient handling and analysis of alerts to differentiate between true and false positives.
- Incident response: Expert assistance in managing and responding to security incidents.
- MDR allows organizations to benefit from expert guidance without needing to hire in-house specialists, thus reducing the burden on internal IT teams and providing a faster and more efficient response to incidents.
Practical IT Security Example
A company deploys EDR across all employee laptops and servers to monitor endpoint activity. Suspicious behavior is detected on one device outside office hours. Through MDR, security analysts investigate the alert, confirm it as a real threat, and initiate containment and remediation without requiring immediate internal IT intervention.
How Can ITAF Help?
ITAF is committed to providing cybersecurity solutions tailored to meet the unique needs of each client. With our expertise in EDR and MDR technologies, we offer services that ensure protection against modern cyber threats. Our team of experienced professionals will:
- Evaluate Your Needs: Conduct a thorough assessment of your current security posture to determine the best EDR solution for your organization.
- Implement and Configure: Deploy and configure EDR across all relevant endpoints, ensuring optimal performance and protection.
- Provide Training: Offer training sessions for your IT staff to help them effectively manage and utilize EDR tools.
- Managed Detection and Response Services
- For organizations seeking an additional layer of protection, ITAF’s MDR services offer:
- 24/7 Monitoring: Continuous surveillance by our Security Operations Center (SOC) analysts who are experts in threat detection and response.
- Incident Response: Rapid response to security incidents, including containment, eradication, and recovery actions.
- Alert Management: Efficient handling of alerts to minimize false positives and ensure real threats are addressed promptly.
- Regulatory Compliance: Assistance in meeting regulatory requirements such as NIS2, ensuring your organization stays compliant with cybersecurity mandates.
Book a free call with our security specialist and enhance your cybersecurity posture.
FAQ
What is EDR?
EDR is a security technology that monitors endpoint devices to detect and respond to cyber threats in real time.
Why is antivirus no longer sufficient?
Antivirus relies on known signatures and may not detect new or advanced threats.
What is MDR used for?
MDR is used to add continuous expert monitoring and response on top of EDR technology.
Does MDR replace internal IT teams?
No. MDR supports internal teams by handling detection and response tasks that require constant monitoring.
How do EDR and MDR relate to NIS2?
They help organizations meet security and resilience requirements defined by the NIS2 directive.